Core Mechanics: Connection Splitting
A proxy server splits your internet session into two distinct TCP connections. Connection 1 runs from your device to the proxy. Connection 2 runs from the proxy to the destination server. These are independent sessions — the destination has no network-level path back to your device.
This architectural split is fundamentally different from a VPN tunnel, which creates one continuous encrypted conduit. The two-connection model is why proxies can operate at massive scale with low overhead: each leg is lightweight and independently managed.
IP Substitution Mechanism
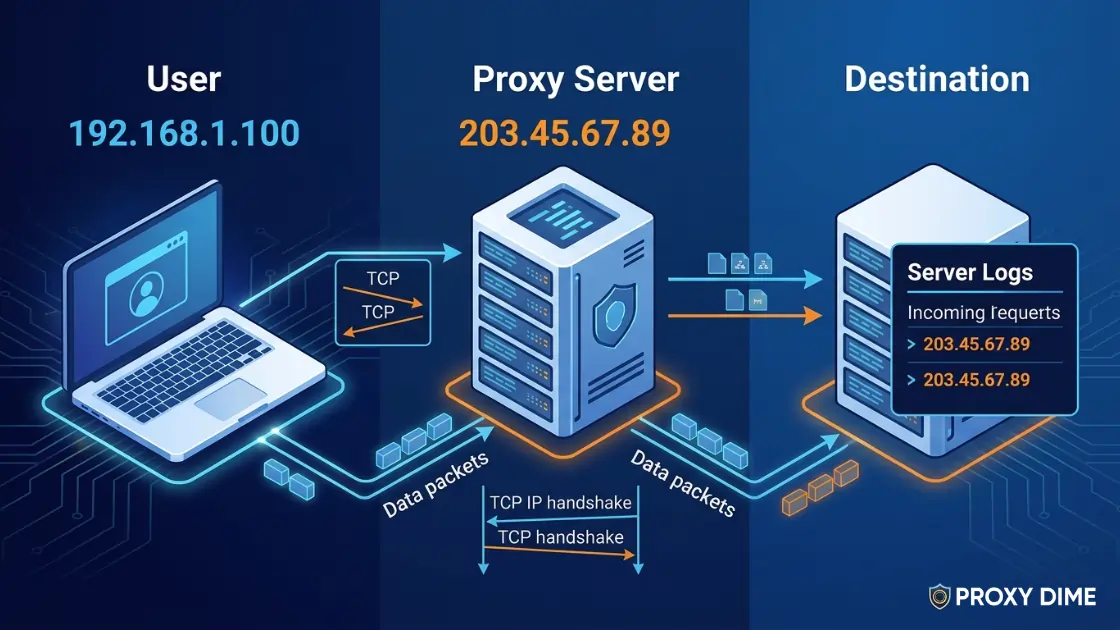
When the proxy opens Connection 2 to the destination server, it uses its own IP address as the source IP in the TCP handshake packets.
The destination server's access logs record the proxy's IP. Your device's IP never appears in any server-side log. This is the foundational IP masking mechanism behind all proxy types — from transparent to elite residential.
HTTP Header Manipulation: The Technical Core
HTTP proxies interact with three critical request headers that control what the destination server knows about you:
| Header | Transparent Proxy | Anonymous Proxy | Elite Proxy |
|---|---|---|---|
| REMOTE_ADDR | Proxy IP (your real IP via XFF) | Proxy IP | Proxy IP |
| HTTP_VIA | Present — lists proxy software | Present — lists proxy | Stripped/absent |
| HTTP_X_FORWARDED_FOR | Your real IP | Absent or proxy IP | Stripped/absent |
Elite proxies remove all three identifying headers, making the connection indistinguishable from a direct user request. SOCKS5 proxies never inject these headers at all — they relay raw packets without any header parsing, which is one reason they offer higher inherent anonymity for non-HTTP traffic.
Protocol Breakdown: HTTP, HTTPS, SOCKS4, SOCKS5
| Protocol | OSI Layer | Traffic Support | Best Use |
|---|---|---|---|
| HTTP | Layer 7 | HTTP/HTTPS only | Web scraping, SEO |
| HTTPS (CONNECT) | Layer 7 | Layer 7 Encrypted HTTPS via tunnel | Secure web tasks |
| SOCKS4 | Layer 5 | TCP only | Basic TCP forwarding |
| SOCKS5 | Layer 5 | TCP + UDP | Gaming, torrents, all protocols |
HTTPS proxies using the CONNECT method add approximately 6% lower RPS and 15–26% higher TTFB versus plain HTTP connections — a modest trade-off for the security of TLS-protected connections on high-value scraping targets.
Caching at the Proxy Layer
HTTP proxies can store server responses locally. When a subsequent request targets the same URL, the proxy serves the cached copy without contacting the origin server.
This eliminates round-trip latency, reduces origin server load, and saves bandwidth — particularly valuable in corporate networks where many users visit the same resources repeatedly. CDN reverse proxies (Cloudflare, Fastly) extend this concept to a global edge network.
Forward vs Reverse Proxy: Architecture
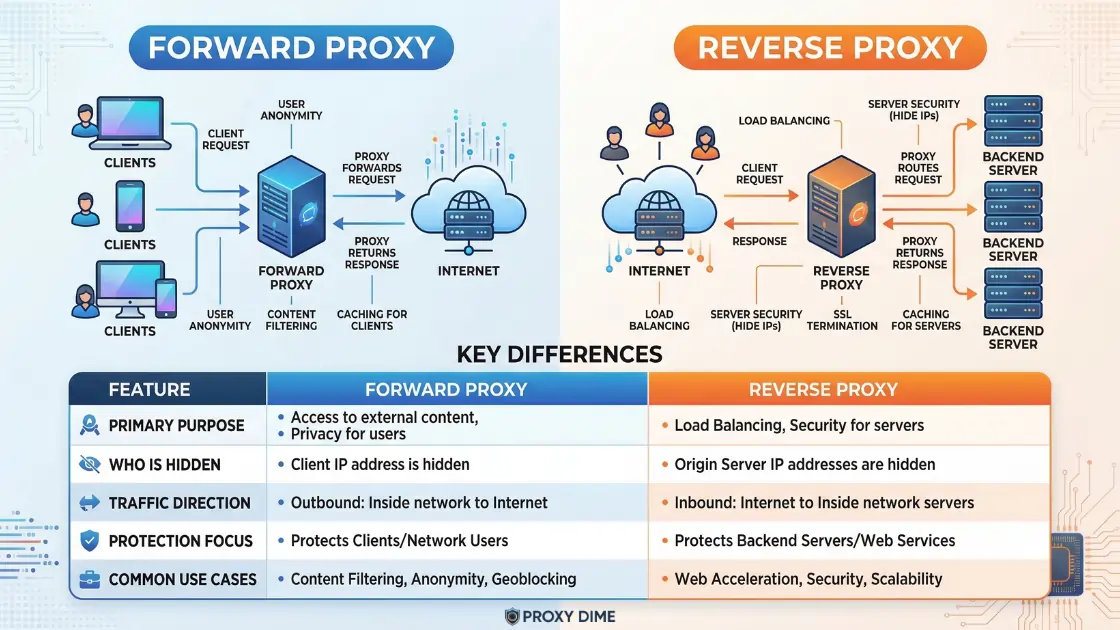
A forward proxy serves clients — it sits between your device and the internet, handling outbound requests on your behalf.
A reverse proxy serves servers — it sits in front of your backend infrastructure and handles all inbound internet traffic. Both use the same IP-substitution and connection-splitting mechanics but serve opposite architectural roles.