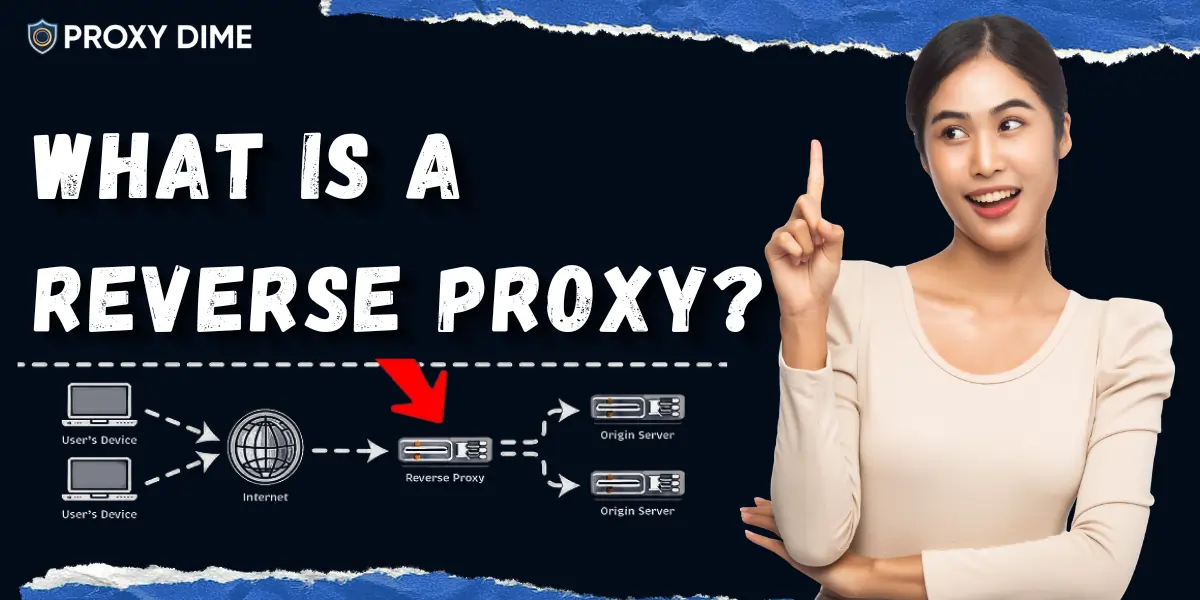
A reverse proxy is a server positioned in front of one or more backend web servers. It intercepts all inbound requests from the internet and acts as the public face of your infrastructure. From a client's perspective, they are communicating directly with your website.
In reality, they are communicating with the reverse proxy, which forwards requests to the appropriate backend server and returns responses. The backend's real IP address is never exposed to the public internet.
This is architecturally the inverse of a forward proxy. A forward proxy protects clients (hides user IPs from servers). A reverse proxy protects servers (hides server IPs from clients). Both use IP substitution and TCP connection splitting — just in opposite directions.
Step-by-Step Request Flow
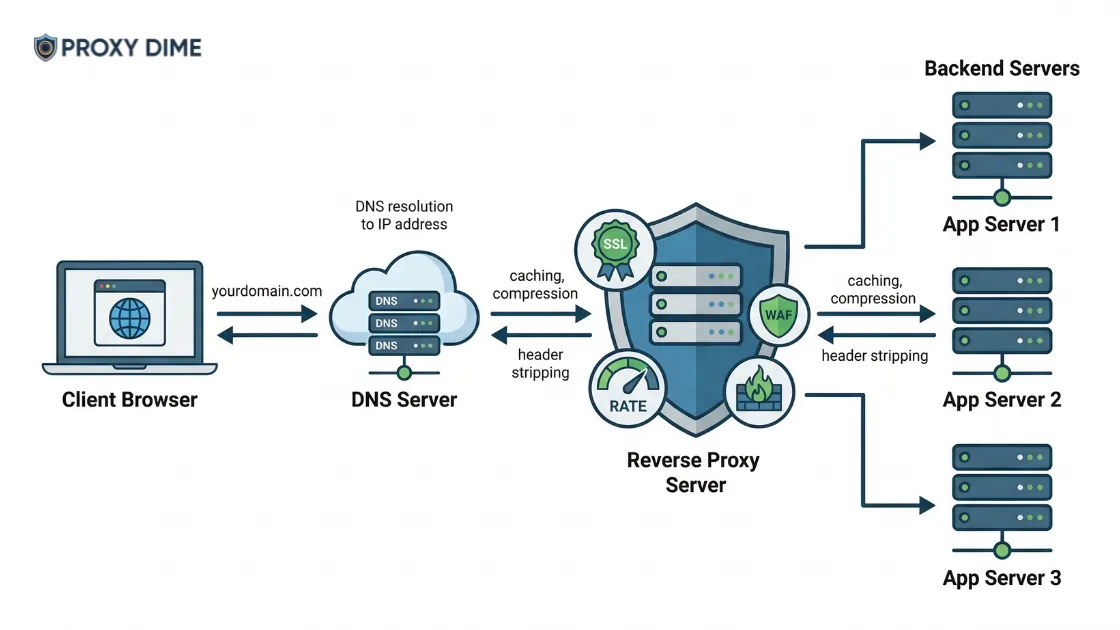
- Client browser sends request to yourdomain.com — DNS resolves to the reverse proxy's IP.
- Reverse proxy receives and evaluates: checks SSL certificate, applies rate limiting, inspects headers, runs WAF rules.
- Based on routing rules (URL path, Host header, load balancing algorithm), the proxy selects a backend server.
- Proxy opens a new connection to the chosen backend and forwards the request.
- Backend processes the request and returns a response to the proxy.
- Proxy optionally caches the response, compresses it, strips internal server headers.
- Client receives the final response — the backend's IP was never exposed.
Core Functions
Popular Reverse Proxy Software
| Software | Type | Notable Users | Key Strength |
|---|---|---|---|
| NGINX | Open-source | Netflix, Cloudflare, LinkedIn | Highest performance; async event model |
| HAProxy | Open-source | GitHub, Reddit, Stack Overflow | Superior load balancing; TCP+HTTP |
| Apache mod_proxy | Open-source | Millions of web servers | Mature; extensive module ecosystem |
| Traefik | Open-source | Docker/Kubernetes ecosystems | Auto service discovery; cloud-native |
| Cloudflare | Cloud service | 19%+ of all websites | Global edge; DDoS + CDN + WAF |
| AWS ALB/CloudFront | Cloud service | Enterprise AWS deployments | Elastic scaling; AWS-native integration |
Forward Proxy vs Reverse Proxy
| Attribute | Forward Proxy | Reverse Proxy |
|---|---|---|
| Positioned in front of | Clients | Servers |
| Protects | Client IP identity | Server IP and infrastructure |
| Configured by | End users / IT admins | DevOps / web server admins |
| Primary use | Anonymity, scraping, geo-bypass | Load balancing, security, SSL termination |